
- CertiK has warned Telegram users of potential exposure to a high-risk security vulnerability.
- The crypto industry is plagued by malicious actors who leverage security weaknesses.
- Users are advised to maintain vigilance to ensure protection against these attacks.
From SIM swap attacks to the deployment of malicious codes and phishing scams, cyberattackers in crypto employ various sophisticated techniques in attacks against industry participants for personal gain. Security vulnerabilities within firms and platforms are also frequently exploited by threat actors, who continuously evolve their tactics to launch attacks on unsuspecting victims.
The resulting apprehension has prompted security experts to ramp up their efforts to protect users from these malicious attacks, one of which has now flagged a recently discovered threat.
CertiK Alerts Telegram Vulnerability
According to blockchain security firm CertiK Alert on Tuesday, April 9, a security vulnerability that poses significant risk to users has been identified on the social messaging platform Telegram.
Sponsored
Identified within the application’s media processing functionality, CertiK emphasized that the “high-risk” threat exposes users to malicious attacks through the platform’s automatic media download feature, and could result in extensive damage if exploited.
CertiK’s warning prompted a response from Telegram. A spokesperson from the company told DailyCoin that the video demonstrating the vulnerability was “a hoax.” The spokesperson added that the report is not backed by reliable information, and the existence of the threat could not be confirmed, nor could a video reproducing the issue be produced upon request.
Despite the response, the highlighted problem has raised security questions across the industry.
What Is the Vulnerability?
The exploit was identified as a “remote code execution” (RCE). This type of security flaw allows cyberattackers to execute arbitrary code on a target system or device remotely, potentially granting an unauthorized third party access to users’ accounts, and allowing them to execute commands or run malicious programs without requiring physical access.
Sponsored
Typically, RCE attacks are executed by sending specially crafted tampered media files, such as images, videos, and GIFs, through a platform, in this case Telegram, which enables the hacker to deploy malware on unsuspecting users’ devices once interacted with.
Are You at Risk?
In its report, the blockchain security platform emphasized that the threat primarily affects users of the desktop Telegram application, and mobile users are largely unaffected. However, Telegram itself denies the existence of the exploit. The saying goes “better safe than sorry though”, so here is what you can do to limit any potential risk on Telegram, or other media platforms.
Those using the automatic media download feature on communication apps may already be exposed and are advised to take extra precautions.
We advise that all users, including those on mobile, employ safety practices across all devices to prevent potential exploits. You can find some preferable settings to use to limit any risk you may face.
How to Stay Safe?
Safeguarding your account from the Telegram vulnerability requires a simple-step modification of the application settings. For this case, we will use Telegram as an example.
Go to Settings: Open the Telegram app on your device and navigate to the settings menu. This is usually accessible by tapping on your profile picture or selecting the three horizontal lines in the app’s top-left corner.
Locate and Tap on “Advanced“: Within the settings menu, identify and select the “Advanced” or “Storage” option. Depending on your device, this may be located towards the bottom of the settings menu. Alternatively, you can use the search box to locate it.
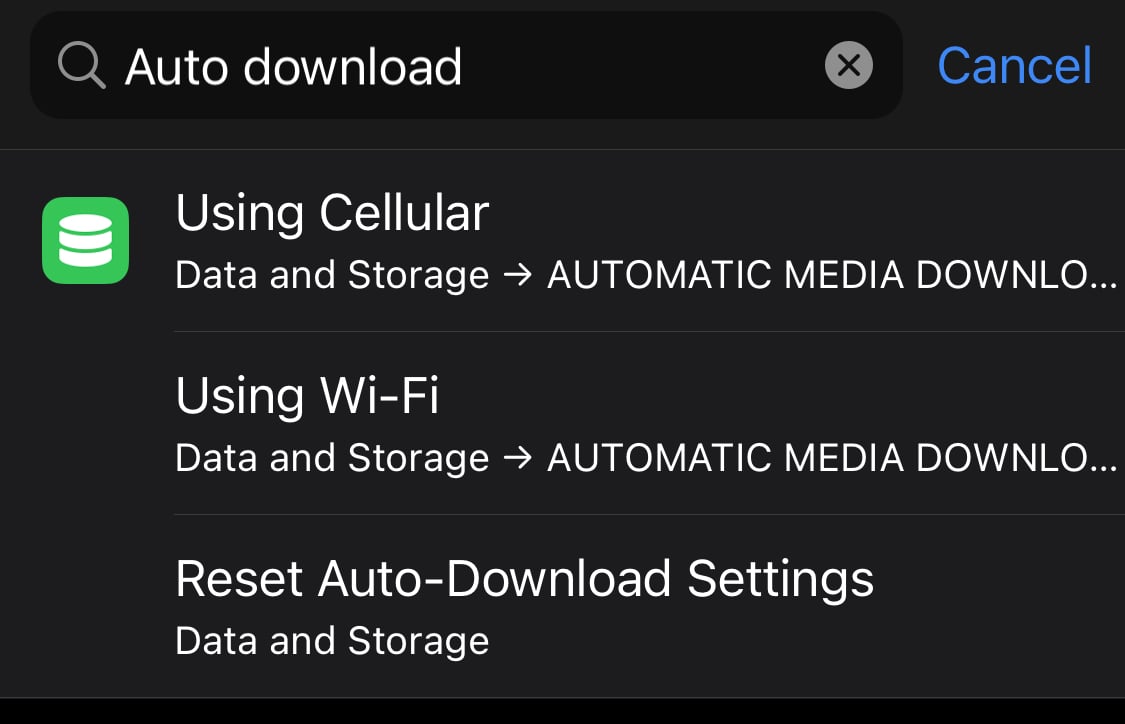
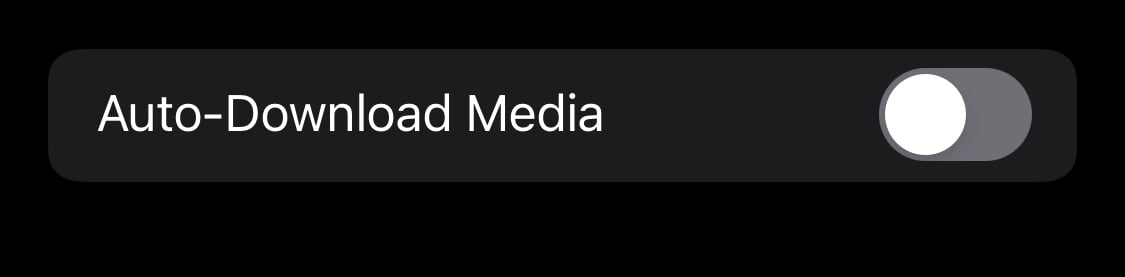
Disable Auto-Download: Under the “Automatic Media Download” section in Advanced, you will find options to control the feature for media such as photos, videos, and files. Select each option to disable the automatic download of such files across all chat types, including private chats, groups, and channels.
Extra Measures: Users are also advised to employ additional security measures, such as heightened vigilance and reinforced security measures, including the use of two-factor authentication and strengthened passwords. This can be done through the ‘Privacy and Security’ option in Telegram.
By following these steps, you can effectively disable the auto-download feature on Telegram, reducing the risk of exposure to potential threats associated with the flagged vulnerability.
On the Flipside
- Several crypto users and projects have fallen victim to fraudulent phishing scams and fake giveaways on Telegram.
- In February 2024, crypto hacks and scams resulted in the loss of over $160 million for investors.
- Earlier this year, CertiK fell victim to a cyber attack on its official X account, underscoring the relentless actions and strengthening tactics employed by malicious actors, even against security experts.
Why This Matters
Telegram is a popular social platform within the crypto industry, hosting thousands of community channels for investors and enthusiasts. With more than 800 million active users, the exploitation of a security vulnerability could lead to far-reaching consequences, underscoring the importance of implementing preventive measures to ensure protection.
Discover more preventive measures against other forms of attacks by reading this article:
How to Prevent a SIM Swap Attack as SEC Falls Prey
Curious about how much time is left until the fourth Bitcoin halving? Read here:
Bitcoin Halving Looms 10 Days Away as BTC Reclaims $70K Mark
