
The world’s largest NFT marketplace, OpenSea, suffered a massive heist this weekend as 254 unique non-fungible tokens (NFTs) were stolen.
Thirty-two OpenSea wallets were emptied of NFT assets during the intrusion, which later appeared to be a phishing attack. The damages to affected parties amounts to an estimated $3 million in total.
What Happened?
Multiple OpenSea users opened their NFT wallets on Saturday only to find them empty, and devoid of valuable assets, including NFTs from the Decentraland, Bored Apes Yacht Club, Cool Cats, and Doodle collections.
Sponsored
More than an hour after the losses were noticed, Opensea reported an ongoing investigation into what “appears to be a phishing attack originating outside of OpenSea’s website.”
Soon after, OpenSea CEO Devin Finzer confirmed that the heist was the outcome of a phishing attack which caused 32 unfortunate users of the platform to sign a malicious payload from the attacker.
It was later determined that the hacker used a standard phishing email mimicking the official mail shared by OpenSea just a day before.
Sponsored
The malicious email urged users to migrate their tokens to the new smart contract before Friday, February 25th, otherwise all existing tokens would expire.
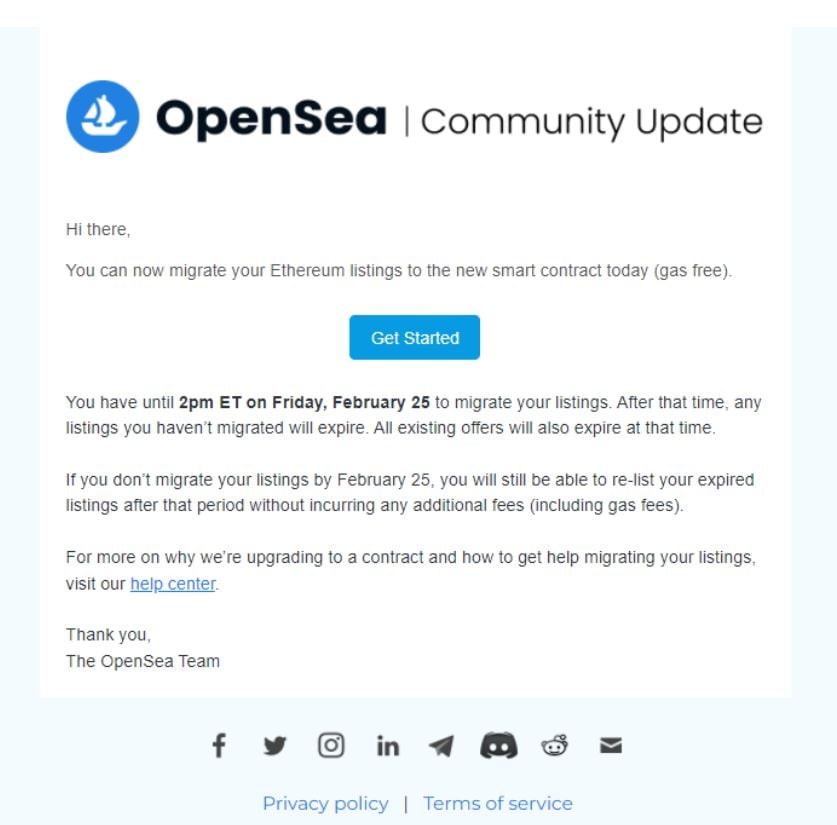
A day before the attack OpenSea announced its smart contract dedicated to removing inactive NFT listings from its platform. Following the upgrade, OpenSea users were required to transfer their old and expired NFT listings hosted on the Ethereum blockchain to a new smart contract. The upgrade was intended to make it difficult for bad actors to trick users into signing orders without them realizing what was happening.
By the end of 2021, the absolute majority of the OpenSea transactions (97%) were carried out on the Ethereum network. The popular marketplace currently offers cross-blockchain support, covering Ethereum, Polygon and Klaytn blockchains.
OpenSea’s CTO Nadav Hollander later commented that none of the malicious orders originated from OpenSea’s website, nor from the official company’s emails. According to him, the orders were unrelated to OpenSea’s migration flow.
The hacker thus exploited users by tricking them to visit an imposter website, where victims signed orders that appeared legitimate to migrate their NFTs to the new OpenSea contract. Instead of secure transfers though, users sent their NFTs to the hacker’s wallet, allowing the bad actors to take control of nearly $3 million worth of non-fungible tokens.
OpenSea later reported that the attack was active for a number of hours, but no malicious activity had been detected since.
The world’s largest NFT marketplace promised that it would continue its investigation and keep users updated. As of Monday 21st, OpenSea has confirmed a narrowed list of 17 victims, contrary to the previously reported 32.
In a meantime, OpenSea users continue to report their drained NFT wallets, and blame the platform for denying an attack and minimizing a problem.
Not the First Time
The phishing attack is not the first time OpenSea users have been abused by malicious actors.
As recently as January 2022, attackers exploited a vulnerability in the world’s largest NFT platform by accessing old NFT listings, buying them for old prices, and then reselling them for their contemporary price, which generated an instant profit of around 332 ETH ($800,000 USD).
